[vc_row][vc_column][vc_column_text]by Eamonn O’Raghallaigh
E-Commerce is defined as the buying and selling of products or services over electronic systems such as the Internet and to a lesser extent, other computer networks. It is generally regarded as the sales and commercial function of eBusiness. There has been a massive increase in the level of trade conducted electronically since the widespread penetration of the Internet. A wide variety of commerce is conducted via eCommerce, including electronic funds transfer, supply chain management, Internet marketing, online transaction processing, electronic data interchange (EDI), inventory management systems, and automated data collection systems. US online retail sales reached $175 billion in 2007 and are projected to grow to $335 billion by 2012 (Mulpuru, 2008).
This massive increase in the uptake of eCommerce has led to a new generation of associated security threats, but any eCommerce system must meet four integral requirements: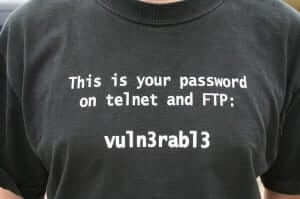
- privacy – information exchanged must be kept from unauthorized parties
- integrity – the exchanged information must not be altered or tampered with
- authentication – both sender and recipient must prove their identities to each other and
- non-repudiation – proof is required that the exchanged information was indeed received (Holcombe, 2007).
These basic maxims of eCommerce are fundamental to the conduct of secure business online. Further to the fundamental maxims of eCommerce above, eCommerce providers must also protect against a number of different external security threats, most notably Denial of Service (DoS). These are where an attempt is made to make a computer resource unavailable to its intended users though a variety of mechanisms discussed below. The financial services sector still bears the brunt of e-crime, accounting for 72% of all attacks. But the sector that experienced the greatest increase in the number of attacks was eCommerce. Attacks in this sector have risen by 15% from 2006 to 2007 (Symantec, 2007).
Privacy
Privacy has become a major concern for consumers with the rise of identity theft and impersonation, and any concern for consumers must be treated as a major concern for eCommerce providers. According to Consumer Reports Money Adviser (Perrotta, 2008), the US Attorney General has announced multiple indictments relating to a massive international security breach involving nine major retailers and more than 40 million credit- and debit-card numbers. US attorneys think that this may be the largest hacking and identity-theft case ever prosecuted by the justice department. Both EU and US legislation at both the federal and state levels mandates certain organizations to inform customers about information uses and disclosures. Such disclosures are typically accomplished through privacy policies, both online and offline (Vail et al., 2008).
In a study by Lauer and Deng (2008), a model is presented linking privacy policy, through trustworthiness, to online trust, and then to customers’ loyalty and their willingness to provide truthful information. The model was tested using a sample of 269 responses. The findings suggested that consumers’ trust in a company is closely linked with the perception of the company’s respect for customer privacy (Lauer and Deng, 2007). Trust in turn is linked to increased customer loyalty that can be manifested through increased purchases, openness to trying new products, and willingness to participate in programs that use additional personal information. Privacy now forms an integral part of any e-commerce strategy and investment in privacy protection has been shown to increase consumer’s spend, trustworthiness and loyalty.
The converse of this can be shown to be true when things go wrong. In March 2008, the Irish online jobs board, jobs.ie, was compromised by criminals and users’ personal data (in the form of CV’s) were taken (Ryan, 2008). Looking at the real-time responses of users to this event on the popular Irish forum, Boards.ie, we can see that privacy is of major concern to users and in the event of their privacy being compromised users become very agitated and there is an overall negative effect on trust in e-commerce. User comments in the forum included: “I’m well p*ssed off about them keeping my CV on the sly”; “I am just angry that this could have happened and to so many people”; “Mine was taken too. How do I terminate my acc with jobs.ie”; “Grr, so annoyed, feel I should report it to the Gardai now” (Boards.ie, 2008).
Learn more about how to protect your data privacy by CLICKING HERE.
Integrity, Authentication & Non-Repudiation
In any e-commence system the factors of data integrity, customer & client authentication and non-repudiation are critical to the success of any online business. Data integrity is the assurance that data transmitted is consistent and correct, that is, it has not been tampered or altered in any way during transmission. Authentication is a means by which both parties in an online transaction can be confident that they are who they say they are and non-repudiation is the idea that no party can dispute that an actual event online took place. Proof of data integrity is typically the easiest of these factors to successfully accomplish. A data hash or checksum, such as MD5 or CRC, is usually sufficient to establish that the likelihood of data being undetectably changed is extremely low (Schlaeger and Pernul, 2005). Notwithstanding these security measures, it is still possible to compromise data in transit through techniques such as phishing or man-in- the-middle attacks (Desmedt, 2005). These flaws have led to the need for the development of strong verification and security measurements such as digital signatures and public key infrastructures (PKI).
One of the key developments in e-commerce security and one which has led to the widespread growth of e-commerce is the introduction of digital signatures as a means of verification of data integrity and authentication. In 1995, Utah became the first jurisdiction in the world to enact an electronic signature law. An electronic signature may be defined as “any letters, characters, or symbols manifested by electronic or similar means and executed or adopted by a party with the intent to authenticate a writing” (Blythe, 2006). In order for a digital signature to attain the same legal status as an ink-on-paper signature, asymmetric key cryptology must have been employed in its production (Blythe, 2006). Such a system employs double keys; one key is used to encrypt the message by the sender, and a different, albeit mathematically related, key is used by the recipient to decrypt the message (Antoniou et al., 2008). This is a very good system for electronic transactions, since two stranger-parties, perhaps living far apart, can confirm each other’s identity and thereby reduce the likelihood of fraud in the transaction. Non-repudiation techniques prevent the sender of a message from subsequently denying that they sent the message. Digital Signatures using public-key cryptography and hash functions are the generally accepted means of providing non-repudiation of communications.
Learn more about how to protect your data privacy by CLICKING HERE.
[/vc_column_text][/vc_column][/vc_row][vc_row content_placement=”middle” css=”.vc_custom_1551967672462{margin-top: 50px !important;margin-bottom: 100px !important;}”][vc_column width=”1/4″][/vc_column][vc_column width=”3/4″][single_cta_ds button_text=”Continue to Part 2″ button_url=”https://digitalmarketingblog.org/security-issues-in-e-commerce-part-2/”][/vc_column][/vc_row]





Recent Comments